In the introductory section of Cyber Security Fundamentals, we examine the central ideas of this discipline. First, we define what cybersecurity is and underscore its vital importance in safeguarding digital assets and data from malicious actors. Next, we explore the evolving scenery of cyber threats, emphasizing the dynamic nature of security challenges. Finally, we establish a foundation by introducing key terminology that will be crucial for understanding the subsequent aspects of cybersecurity. This section provides a solid base for readers to delve deeper into the world of cyber security.
The Evolution of Cyber Threats
The evolution of cyber threats represents a dynamic and ongoing process in the realm of information security. Over time, cyber threats have transformed from relatively simple, isolated attacks to sophisticated, organized, and pervasive challenges. Initially characterized by viruses and basic malware, they have now evolved into complex and multifaceted threats, including ransomware, advanced persistent threats (APTs), and nation-state-sponsored attacks. These threats have adapted to exploit vulnerabilities in emerging technologies such as the Internet of Things (IoT), cloud computing, and artificial intelligence. As the threat scenery continues to evolve, organizations and individuals must remain vigilant, stay updated on the latest threats, and implement robust cybersecurity measures to protect sensitive data and critical systems in this ever-changing environment.
Cybersecurity awareness
Cybersecurity awareness is of paramount importance in today's digital age as it empowers individuals and organizations to recognize, prevent, and respond to cyber threats effectively. By educating users about safe online practices, it reduces the likelihood of falling victim to cyberattacks, such as phishing and malware. Additionally, it promotes a culture of vigilance and responsible data handling, ultimately safeguarding sensitive information and preserving the trust and reputation of both individuals and businesses in an increasingly interconnected world.
Common Cyber Threats
Malware, short for "malicious software," encompasses a wide range of malicious programs designed to infiltrate computer systems and compromise their integrity. This category includes viruses, which attach themselves to legitimate files, Trojans, which disguise themselves as legitimate software, worms that self-propagate through networks, and ransomware, which encrypts files and demands a ransom for decryption. Malware can cause data loss, system damage, and financial harm.
Social engineering attacks rely on psychological manipulation to deceive individuals into revealing sensitive information or performing actions that compromise security. Phishing involves deceptive emails or websites that impersonate trusted entities to extract login credentials or personal information. Spear phishing targets specific individuals or organizations, often using personalized information to enhance the credibility of the attack. Social engineering can lead to unauthorized access, identity theft, or financial fraud.
Denial of Service attacks aim to disrupt the availability of a system or network by overwhelming it with excessive traffic or resource requests. This renders the target system unresponsive, making it inaccessible to legitimate users. Distributed Denial of Service (DDoS) attacks involve multiple compromised devices coordinated to launch a massive and coordinated assault. DoS attacks can lead to downtime, loss of business, and reputational damage.
Data breaches involve unauthorized access to sensitive or confidential information, which is then exposed, stolen, or leaked. These breaches can occur due to various vulnerabilities, such as weak passwords, unpatched software, or insider threats. The consequences of data breaches can be severe, including financial losses, regulatory penalties, and harm to an organization's reputation. Protecting against data breaches is a significant priority in information security.
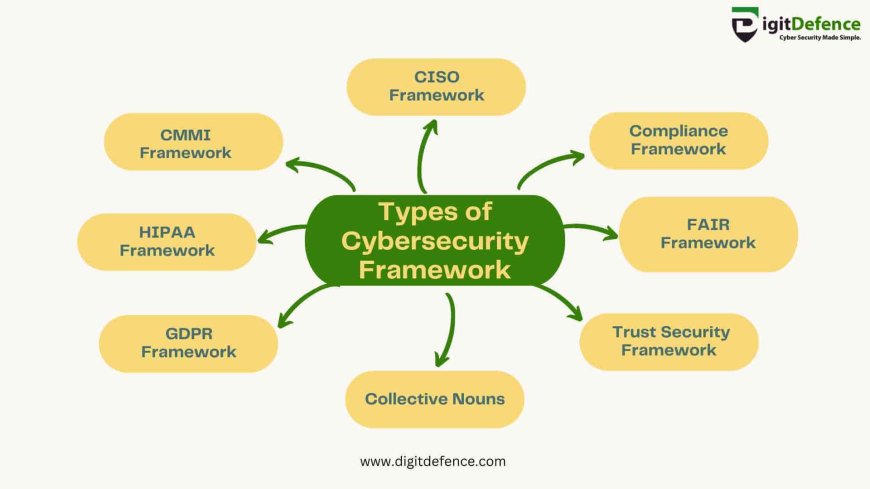
Types of Cybersecurity Frameworks
NIST Cybersecurity Framework (CSF): The NIST CSF is a widely recognized framework that provides a structured approach to managing and improving an organization's cybersecurity posture. It encompasses functions such as Identify, Protect, Detect, Respond, and Recover, offering a comprehensive IT security framework.
ISO/IEC 27001: This international standard outlines the requirements for establishing, implementing, maintaining, and continually improving an information security management system (ISMS). It is a robust information security framework widely used for securing sensitive data.
COBIT (Control Objectives for Information and Related Technologies): COBIT is a framework developed by ISACA, focusing on the governance and management of enterprise IT. It provides a set of controls and best practices for IT security frameworks, ensuring alignment with business objectives.
CIS Critical Security Controls: The Center for Internet Security (CIS) offers a set of best practices known as the Critical Security Controls. These controls prioritize various security measures to enhance an organization's overall cybersecurity posture.
PCI DSS (Payment Card Industry Data Security Standard): PCI DSS is a compliance framework designed to secure payment card transactions. It includes a set of security requirements that organizations processing credit card information must adhere to, ensuring the protection of sensitive financial data.
ITIL (Information Technology Infrastructure Library): While not solely focused on cybersecurity, ITIL provides a framework for IT service management. It includes practices for managing IT services, aligning them with business needs, and maintaining a secure and efficient IT environment.
Security Measures
Security Measures are fundamental aspects of information security, playing a pivotal role in safeguarding data and systems from various threats.
-
Passwords and authentication mechanisms are the first lines of defence against unauthorized access. They ensure that only authorized individuals can access sensitive information and systems.
-
Encryption is the process of encoding data to protect its confidentiality. It prevents unauthorized access by making data unreadable without the correct decryption key, securing information during transmission and storage.
-
Firewalls act as barriers between trusted and untrusted networks, controlling incoming and outgoing network traffic. Intrusion Detection Systems (IDS) monitor network traffic for suspicious activity and potential threats, providing an additional layer of security.
-
Patch management is essential for keeping software and systems up to date with the latest security fixes. Regularly applying patches helps protect against known vulnerabilities and reduces the risk of exploitation.
-
Backups are crucial for ensuring data recovery in case of accidental data loss, hardware failures, or disasters. Disaster recovery plans outline the procedures and resources necessary to restore operations after a catastrophic event.
These security measures collectively contribute to the overall security posture of an organization, helping to mitigate risks, maintain data integrity, and ensure the confidentiality and availability of critical information and systems.
Network Security
Network segmentation involves dividing an organization's network into smaller, isolated segments to enhance security. By restricting lateral movement within the network, it can minimize the potential impact of a security breach. Proper segmentation helps in containing threats and maintaining the confidentiality and integrity of sensitive information.
Virtual Private Networks (VPNs) play a crucial role in securing data communication. VPNs establish encrypted and secure connections over untrusted networks, such as the Internet. They are invaluable for ensuring the privacy and integrity of data transmitted between remote users and corporate networks, making them essential for remote work and protecting sensitive information.
With the prevalence of wireless networks, safeguarding these connections is imperative. Wireless network security involves measures like encryption, strong authentication protocols, and secure configurations for Wi-Fi routers. These measures are essential for protecting against unauthorized access and eavesdropping, ensuring the confidentiality and availability of wireless data and resources.
Operating System Security
Operating System Security is a fundamental element within the broader realm of information security. It focuses on safeguarding the core software that manages computer hardware and facilitates user interactions. This component is crucial because the operating system serves as the foundation for all other software applications and processes, making it a prime target for malicious actors.
Key aspects of Operating System Security include access control mechanisms to restrict user privileges, regular software updates to patch vulnerabilities, and the implementation of security configurations that align with best practices. These measures are essential in reducing the risk of unauthorized access, data breaches, and system compromises.
Operating System Security also encompasses securing user accounts and passwords, managing file and directory permissions, and employing intrusion detection and prevention systems to monitor and respond to suspicious activities. As the operating system plays a central role in the overall IT environment, ensuring its security is a critical prerequisite for safeguarding sensitive data, maintaining system availability, and preventing potential security breaches.
Web Security
Web Security is a crucial aspect of information security that focuses on safeguarding online activities and interactions. It encompasses the following key components:
Secure web browsing involves implementing measures to protect users from online threats while they access websites and navigate the internet. This includes using up-to-date web browsers, regularly applying security patches, and employing antivirus software to defend against malicious websites, malware, and phishing attacks. Secure browsing also entails user education to recognize and avoid potentially harmful online content.
Web applications are frequently targeted by cybercriminals, making it essential to secure them. This involves following best practices in web development, such as input validation, data encryption, and secure coding techniques to prevent common vulnerabilities like Cross-Site Scripting (XSS) and SQL injection. Employin